be.Safe XDR
Full Network Visibility
Take control of your network infrastructure with real-time traffic analysis. Detect anomalies, optimize performance, and make data-driven decisions with a platform that integrates seamlessly with any vendor.
The control your network needs

As organizations move to the cloud, they often lose visibility across their networks. Network Traffic Analysis (NTA) restores control through real-time telemetry, intelligent analytics, and customizable dashboards that deliver full visibility across the entire:
-
- Multi-vendor platform compatible with devices from any network vendor.
- Scalable, multi-tenant cloud SaaS architecture for organizations of any size.
- Machine learning enables real-time detection of anomalous behavior.
- Unlimited, customizable dashboards accessible to non-technical users.
- Forensic analysis with interactive tools for real-time and historical.
Your network as a strategic asset

Digital transformation has turned network infrastructure into the central nervous system of modern organizations. However, paradoxically, the more critical the network becomes, the less visibility IT teams have into what is actually happening within it.
The widespread adoption of cloud services, hybrid work, and the proliferation of connected devices have fragmented the traditional network perimeter. As a result, traffic now flows across data centers, public clouds, remote offices, and mobile devices, creating blind spots that make both troubleshooting and anomaly detection increasingly difficult.
The Network Traffic Analysis market is experiencing sustained growth, driven by three key factors: the exponential rise in cyberthreats that use the network as an attack vector, the adoption of Zero Trust architectures that require fine-grained visibility, and the need to optimize infrastructure investments based on real data.
Organizations recognize that they can no longer protect or optimize what they cannot see. Network visibility is no longer a desirable add-on, but a fundamental capability. IT teams need tools that not only capture data but also transform it into actionable insights identifying bottlenecks before they impact the business, detecting shadow IT, planning future capacity, and reducing incident resolution times.
The challenge today is not a lack of data, but the ability to process, correlate, and present it in a way that enables every role within the organization to make informed decisions.
What are the important points related to Network Traffic Analysis?
Full multi-vendor visibility
The platform ingests device telemetry from any vendor including routers, switches, firewalls, and endpoints. This universal compatibility eliminates data silos and provides a unified view of the entire network infrastructure.
Applied Artificial Intelligence (AI)
Machine learning algorithms learn normal network behavior and automatically detect anomalies. The system identifies deviations in traffic patterns, bandwidth usage, and user activity without the need for manual configuration.
Access across the organization
Designed with business-oriented language, not just technical terminology. Customizable dashboards enable different departments to access relevant information, democratizing network data across the organization.

From visibility to action
The system doesn’t just detect it acts. Configurable alerts notify teams of situations that require attention. Integration with SD-WAN enables automated responses, reducing the time from detection to mitigation.
Understanding Network Traffic Analysis
Network Traffic Analysis (NTA) is a technology discipline that enables organizations to regain visibility into their communications infrastructure. As corporate networks evolve from simple topologies to complex ecosystems spanning multiple locations, cloud environments, and device types, NTA provides the tools to understand what is actually happening across the network.
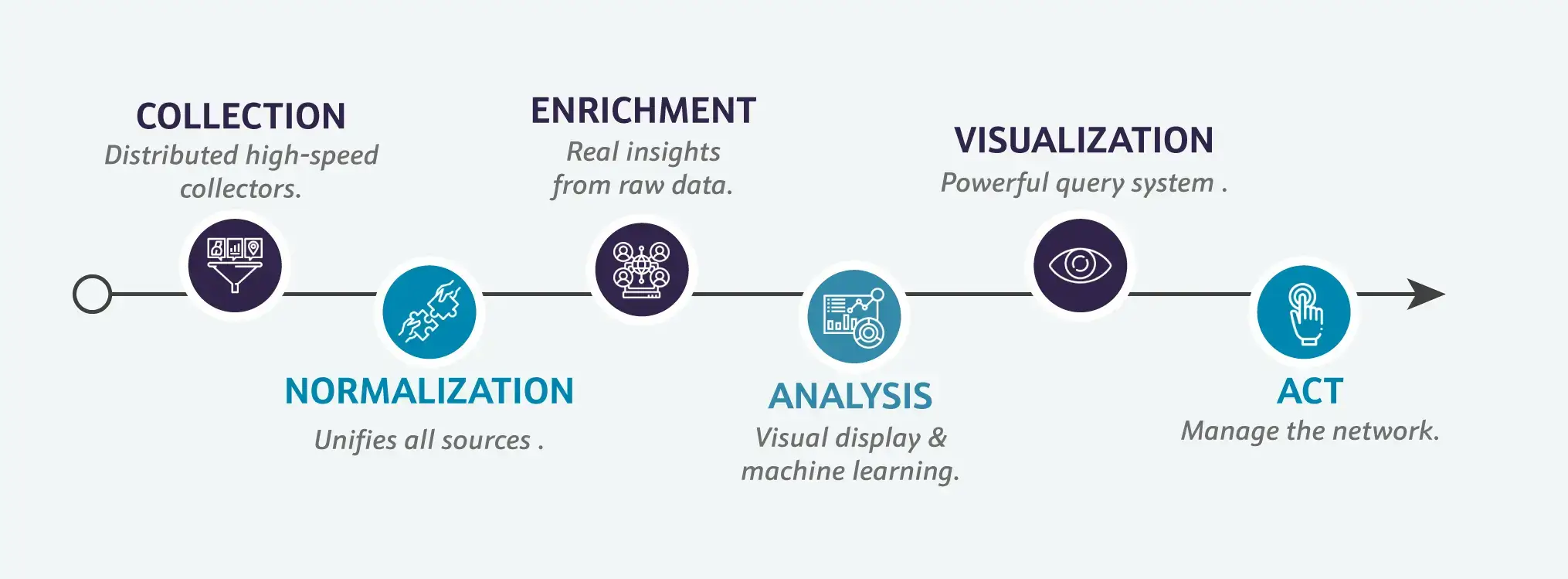
Six-Component Architecture
A modern NTA solution operates through six distinct technical processes:
1- Collection: Continuous capture of telemetry data and network traffic in real time. The system ingests data from multiple sources, including NetFlow, sFlow, IPFIX, device logs, and traffic metadata.
2- Normalization: Data from different vendors and formats is standardized into a common model, enabling comparison and correlation regardless of its source.
3- Enrichment: Raw data is enhanced with external intelligence, including IP geolocation, domain reputation, application classification, and known threat intelligence feeds.
4- Analysis: This is where the platform’s intelligence resides. Machine learning algorithms establish baselines of normal behavior and detect deviations. The system learns usage patterns by user, application, location, and time.
5- Visualization: Processed data is presented through dashboards and customizable reports. Users can create tailored views based on their needs, from detailed technical metrics to high-level business indicators.
6- Action: The system generates configurable alerts when it detects situations that require attention. Alerts can be integrated with ticketing systems, notifications, or can trigger automated responses.
Key Use Cases
NTA (Network Traffic Analysis) addresses multiple operational and business needs:
- Accelerated troubleshooting: Rapid identification of bottlenecks, latency, and connectivity issues through traffic flow visualization and pattern analysis.
- Shadow IT control: Detection of unauthorized applications and non-corporate cloud services used without IT approval.
- Infrastructure optimization: Analysis of usage trends to properly size network links, identify underutilized capacity, and plan future investments.
- Forensic analysis: Use of historical data to investigate past incidents, reconstruct events, and determine their scope.
- Early anomaly detection: Identification of unusual behavior that may indicate performance issues or suspicious activity before it impacts the business.
Scalability and Deployment
Today’s NTA solutions are delivered as cloud (SaaS) services, eliminating the need for dedicated infrastructure. Built on a multi-tenant, hierarchical architecture, they scale seamlessly across organizations of all sizes from small and medium-sized businesses to large enterprises with geographically distributed operations.
Solution & Teldat Products
Teldat Network Traffic Analysis (NTA) – be.Safe XDR
Teldat delivers Network Traffic Analysis (NTA) capabilities through its be.Safe XDR platform, part of the broader Teldat solutions ecosystem. This approach differentiates Teldat from competitors offering standalone solutions, delivering network visibility as part of a comprehensive network and security management strategy.

Solution Architecture

be.Safe XDR is delivered as a cloud (SaaS) service, eliminating the need for investment in dedicated infrastructure. Built on a hierarchical, multi-tenant architecture, the platform enables organizations to:
- Group users and devices by organization or region.
- Filter data by site, department, or user.
- Manage multiple clients from a single instance (ideal for MSP’s)
- Scale horizontally based on organizational needs.
Universal compatibility
Unlike proprietary solutions, be.Safe XDR ingests device telemetry from any network vendor. The platform collects data streams from routers, switches, firewalls, and endpoints regardless of brand. This is particularly valuable in multi-vendor environments where diverse devices coexist.
Teldat ecosystem
be.Safe XDR operates in conjunction with Cloud Net Manager modules:
- Analyzer: Monitoring environment for WAN, SD-WAN, LAN, WLAN, and UTM networks.
- Manager: Lifecycle management for Zero Touch Provisioning (ZTP) devices.
- SD-WAN Controller: Network management based on a global data model.
This integration allows visibility data to directly inform network configuration and optimization decisions.

Intelligent Analysis

The be.Safe XDR analysis engine leverages Machine Learning (ML) techniques to:
- Establish baselines of normal behavior by user, application, and location.
- Detect anomalies in traffic patterns without predefined rules.
- Identify growth trends to support future capacity planning.
- Automatically classify applications and protocols.
Visualization and Reporting
The platform provides unlimited flexibility for designing dashboards and reports:
- Customizable widgets with technical and business metrics.
- Dashboards enriched with text, images, and external data sources.
- Automated report scheduling.
- Export to multiple formats.
Automated response
Beyond visibility, be.Safe XDR enables organizations to configure automated actions:
- Configurable alerting system with multiple severity levels.
- Email and SMS notifications, integrated with ticketing systems.
- Integration with SD-WAN for automated network responses.
- Configurable response policies: notification, mitigation, or remediation.
Key differentiators
- Business-oriented language: Accessible beyond technical teams, across the entire organization.
- Agentless deployment: No software installation required on endpoints.
- Unlimited historical data: Configurable data retention for forensic analysis.
- Proactive support: Continuous monitoring with early alerts.

Network Traffic Analyisis (NTA) – Use cases
Troubleshooting in distributed networks
Reduce incident resolution time through centralized visibility across all sites and network links.
Shadow IT control and compliance
Identify unauthorized cloud applications and non-corporate services used without IT approval.
Rapid troubleshooting in distributed networks
Reduce incident resolution time through centralized visibility across all sites and network links.
Challenge
Organizations with multiple sites face a critical challenge: when users report connectivity or performance issues, IT teams often lack the visibility needed to quickly identify the root cause. The issue may lie in the WAN link, the local LAN, a specific device, or an external cloud service. Traditionally, troubleshooting requires accessing multiple devices, reviewing logs from different systems, and manually correlating disparate data. This process consumes hours of specialized effort while users continue to experience service degradation.
The situation is further complicated in multi-vendor environments, where each vendor provides its own tools. IT teams must navigate multiple interfaces and data formats, making event correlation more difficult and prolonging resolution times.
Solution

The implementation of Network Traffic Analysis (NTA) provides a unified dashboard delivering real-time visibility across the entire network infrastructure. When an incident arises, IT teams have immediate access to:
- Traffic flow maps that identify where bottlenecks are occurring.
- Historical metrics to determine whether the issue is new or recurring.
- Trend analysis to anticipate link saturation.
- Automatic correlation of events from multiple sources.
The system automatically detects anomalies and proactively alerts teams before users report issues. Troubleshooting shifts from a reactive to a predictive approach.
Why Teldat?
be.Safe XDR integrates Network Traffic Analysis (NTA) visibility with Teldat’s infrastructure management capabilities. This unified platform enables IT teams not only to diagnose issues but also to apply corrective actions directly from a single environment—reducing the overall resolution cycle.
Shadow IT control and compliance
Identify cloud applications and non-corporate services used without IT authorization.
Challenge
The Shadow IT phenomenon represents one of the greatest risks facing modern organizations. Well-intentioned employees often adopt cloud tools, storage services, and productivity applications outside official IT channels. While these tools can improve individual productivity, they also introduce significant risks for the organization.
Sensitive corporate data may end up in unapproved cloud services, beyond the company’s control and outside established security policies. In addition, many industries are subject to strict regulations that require control over where data resides and how it is transmitted. Without visibility into which applications and services are actually in use, IT and security teams operate blindly. Compliance audits become guesswork, and risks often remain hidden until incidents occur.
Solution

Network Traffic Analysis (NTA) provides full visibility into all applications and cloud services accessed across the network. The system enables:
- Automatic traffic classification by application and category.
- Identification of non-corporate cloud services (e.g., personal storage, social networks).
- Measurement of data transfer volumes per service.
- Generation of compliance reports with clear usage evidence.
This enables IT teams to make informed decisions blocking high-risk services, providing approved alternatives, and enforcing usage policies based on real data.
Why Teldat?
be.Safe XDR combines Shadow IT detection with integrated control capabilities. By leveraging the be.Safe firewall, policies can be enforced directly from the platform, closing the loop from detection to remediation.
Network investment optimization
Optimal infrastructure sizing through usage trend analysis and future demand forecasting.
Challenge
Infrastructure investment decisions in traditional networks are often driven by subjective perceptions or reactive responses to issues that have already occurred. IT teams increase bandwidth when users complain or upgrade devices after failures, without a clear understanding of actual needs. This reactive approach leads to two opposing outcomes: overprovisioned infrastructure that drives unnecessary costs, or underprovisioned environments that impact business performance. Without objective data on usage patterns, growth trends, and demand peaks, optimizing investment becomes increasingly difficult.
In addition, the shift toward hybrid and multicloud environments further complicates capacity planning. Traffic no longer flows predictably between sites and central data centers, but is dynamically distributed across multiple cloud destinations.
Solution

Network Traffic Analysis (NTA) transforms capacity planning into a data-driven exercise. The platform provides:
- Historical usage trend analysis by link, site, and application.
- Growth forecasts based on observed patterns.
- Identification of underutilized or overprovisioned links.
- Estimated capacity run-out dates.
- Quality of service (QoS) metrics by connectivity provider.
This information enables IT teams to justify investments with concrete data, negotiate connectivity contracts based on actual usage, and anticipate future needs before they impact the business.
Why Teldat?
be.Safe XDR stores unlimited historical data, enabling long-term trend analysis. Integration with be.Analyzer provides detailed performance metrics by link and carrier, essential for negotiating with service providers.
Read our latest Blog Posts
From Firewalls to XDR: A Historical Journey Through Enterprise Cybersecurity
The Ever-Evolving Cyber Threat Landscape Over the past few decades, cybersecurity has undergone a profound transformation in response to an increasingly interconnected and digitalized world. What once revolved around basic perimeter defenses—such as traditional...
Quantum computing and the path towards secure Quantum SD-WAN
Quantum computing is no longer confined to research laboratories; it has emerged as a technological force with the potential to transform—and potentially undermine—digital security as we know it. Its rapid advancement is accelerating the arrival of a future in which...
Why the world is now looking to Europe to lead cybersecurity?
Over the past decade, cybersecurity has evolved from a specialized technical field into a core pillar of national resilience and executive responsibility. Today, boards and public administrations worldwide face a simple yet crucial question: Who can we trust to...