BLOG
Unified SD-Branch and Security
Enterprise networks have outgrown the model where connectivity and protection live in separate silos. Branch offices now host cloud workloads, hybrid workers, IoT devices, and a constant flow of SaaS traffic that never touches the data center. Trying to secure that traffic with a stack of point products bolted on top of an SD-WAN edge has become slow, expensive, and...
Kategorien
AI-driven threat detection & response in the age of intelligent cyberattacks
In a world where artificial intelligence is advancing by leaps and bounds, organizations face a significant increase in the volume and complexity of cyberattacks. The need for AI-driven threat detection and response has never been more urgent. One of the most notable...
Cloud Native SASE architecture protecting your business in a borderless world
Not long ago, keeping a corporate network secure was straightforward. Employees worked from the office. Apps lived in the data centre. IT drew a clear line between “inside” and “outside.” A firewall at the door and a VPN for the occasional remote worker done. "That...
Active Directory – Authentication: The key to secure, frictionless access
In an increasingly identity-driven world, giving users secure, controlled, and efficient access to systems is a top priority for any organization. Authentication has come a long way from simple local passwords to complex ecosystems that combine directories,...
Generative AI as an attack vector: a new frontier in Cybersecurity
Generative Artificial Intelligence (Generative AI) is redefining the cybersecurity landscape in ways that go far beyond the purely technical. Its impact extends to the strategic level, affecting the digital and geopolitical sovereignty of companies and governments...
Zero Touch Provisioning (ZTP) at scale: How SD‑WAN automation enables large‑scale network deployments?
Zero Touch Provisioning (ZTP) has become a central concept in modern network architecture discussions, particularly in environments adopting SD‑WAN and automation-driven operations. In its simplest explanation, ZTP allows a network device to be shipped directly to a...
Why industrial OT security specialization is no longer optional
The factory floor is now a cyber battlefield. As industrial environments become increasingly connected, the traditional approach of treating Operational Technology (OT) security as an afterthought—or worse, as an extension of IT security—is proving dangerously...
All 5G’s Are Born Equal, But Some Are More Equal Than Others
When 5G entered the public conversation, it did so with grand ambitions. Ultra-fast speeds. Near-zero latency. A technology poised to reshape everything from factory automation to healthcare delivery. For most users, however, the experience boiled down to something...
What is the CCN and how does it relate to the ENS, the CPSTIC Catalog, and cybersecurity products?
In Spain, public-sector cybersecurity is structured around several key concepts: the National Cryptology Center (CCN), the National Security Framework (ENS), the CPSTIC Catalog, and the Qualified and Approved cybersecurity products listed within it. Although closely...
Connected trains, accelerated defense: real-time Cybersecurity for embedded networks
In the 21st century, trains have evolved far beyond steel and track gauge. Modern rolling stock increasingly incorporates one or more IP networks that are growing ever more complex. Connected passengers, smart sensors, and critical operating systems now converge...
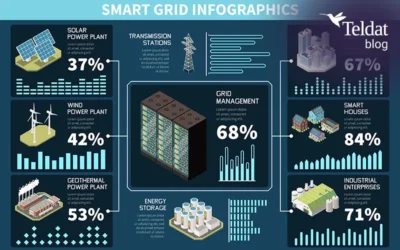
Cybersecurity for Smart Grids: Protecting the energy infrastructure of the future
The digital transformation of the electricity sector has accelerated the adoption of Smart Grids: advanced energy infrastructures that integrate distributed generation, active demand response systems, and real-time bidirectional communication mechanisms enabled by...
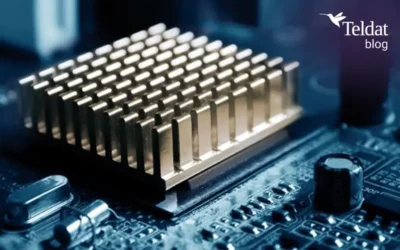
Heat Transfer in network equipment
Heat transfer is a crucial part of how any electronic equipment works. When devices are operating, their internal components generate heat, and that heat needs to be dissipated in a controlled way. Doing so ensures safe and reliable operation, helps maintain optimal...
From Firewalls to XDR: A Historical Journey Through Enterprise Cybersecurity
The Ever-Evolving Cyber Threat Landscape Over the past few decades, cybersecurity has undergone a profound transformation in response to an increasingly interconnected and digitalized world. What once revolved around basic perimeter defenses—such as traditional...