Safe access with Teldat’s ZTNA
Teldat’s Zero Trust solution provides secure and controlled access to corporate applications and resources, with flexible cloud or on-site deployment to meet the needs of each organization.
VPN-free, identity-based access
Teldat’s ZTNA solution protects corporate applications and resources from unauthorized access through an identity-based model, continuous verification, and granular control, adapting to hybrid environments without relying on VPNs:
-
- Zero Trust security: continuous verification for every session.
- Reduced attack surface: applications are not exposed to the Internet.
- Context- and device-based control: identity, risk, and device posture.
- Improved user experience: transparent access to applications and resources.
- Compliance and auditing: full traceability, logging, and reporting.
Secure access in the Zero Trust Era
Remote access and access to corporate applications have changed dramatically in recent years. The disappearance of the traditional security perimeter, the adoption of cloud services, and the rise of hybrid working have highlighted the limitations of classic models based on VPNs and implicit trust within the network.
In this new scenario, users, devices, and applications connect from a wide range of locations and environments, increasing the risk of unauthorized access and expanding the attack surface. Organizations need to protect access without exposing their applications to the Internet and without assuming that everything happening inside the network is safe.
The Zero Trust Network Access (ZTNA) approach was developed in response to these challenges, replacing the traditional access model with one based on identity, context, and continuous verification. Instead of granting broad access to the network, ZTNA provides authorized access only to the specific applications and resources required, significantly reducing the impact of potential attacks.
Current ZTNA solutions aim to improve security without sacrificing the user experience by providing transparent access, granular policies, and centralized management. In addition, they enable organizations to adapt to hybrid and distributed environments while meeting today’s requirements for control, compliance, and flexibility.

What are the important points related to Zero Trust Network Access (ZTNA)
Identity-based access
Access control is based on the user’s identity rather than the network identity. The solution integrates with identity providers and SSO to enforce strong authentication and ensure that only authorized users can access each resource.

Continuous device assessment
Before and during each session, the device status is verified to check its security posture. This allows policies to be applied based on compliance, reducing risks from untrusted or poorly protected equipment.

Dynamic policies per session
Access policies are dynamically evaluated during each session, taking into account the user, device, context, and risk level. As a result, access can be monitored and adjusted in real time, limiting the impact of potential attacks.
Minimal access to applications
Access is granted only to specific applications and services, rather than to the entire network. This microsegmentation approach reduces the attack surface and prevents lateral movement in the event of a security breach.
The evolution of application access
For years, the traditional model for accessing corporate systems relied on a well-defined perimeter: once a user connected to the network, usually through a VPN tunnel, they were considered trustworthy. However, in a context where applications are distributed, users work from anywhere, and devices are not always under the direct control of the organization, this approach is becoming increasingly ineffective.
Today, access takes place from multiple locations, using different devices, and to applications hosted in both local and cloud environments. In this scenario, implicitly trusting a user or connection creates significant risk, as unauthorized access may lead to lateral movement, exposure of internal resources, or other far-reaching consequences.
The Zero Trust approach emerged in response to this shift. Its core principle is simple: never trust by default and always verify. Instead of assuming that a user is trustworthy simply because they are connected, every access request is evaluated based on identity, context, and session conditions.
Within this model, Zero Trust Network Access (ZTNA) redefines how users access corporate applications and resources.
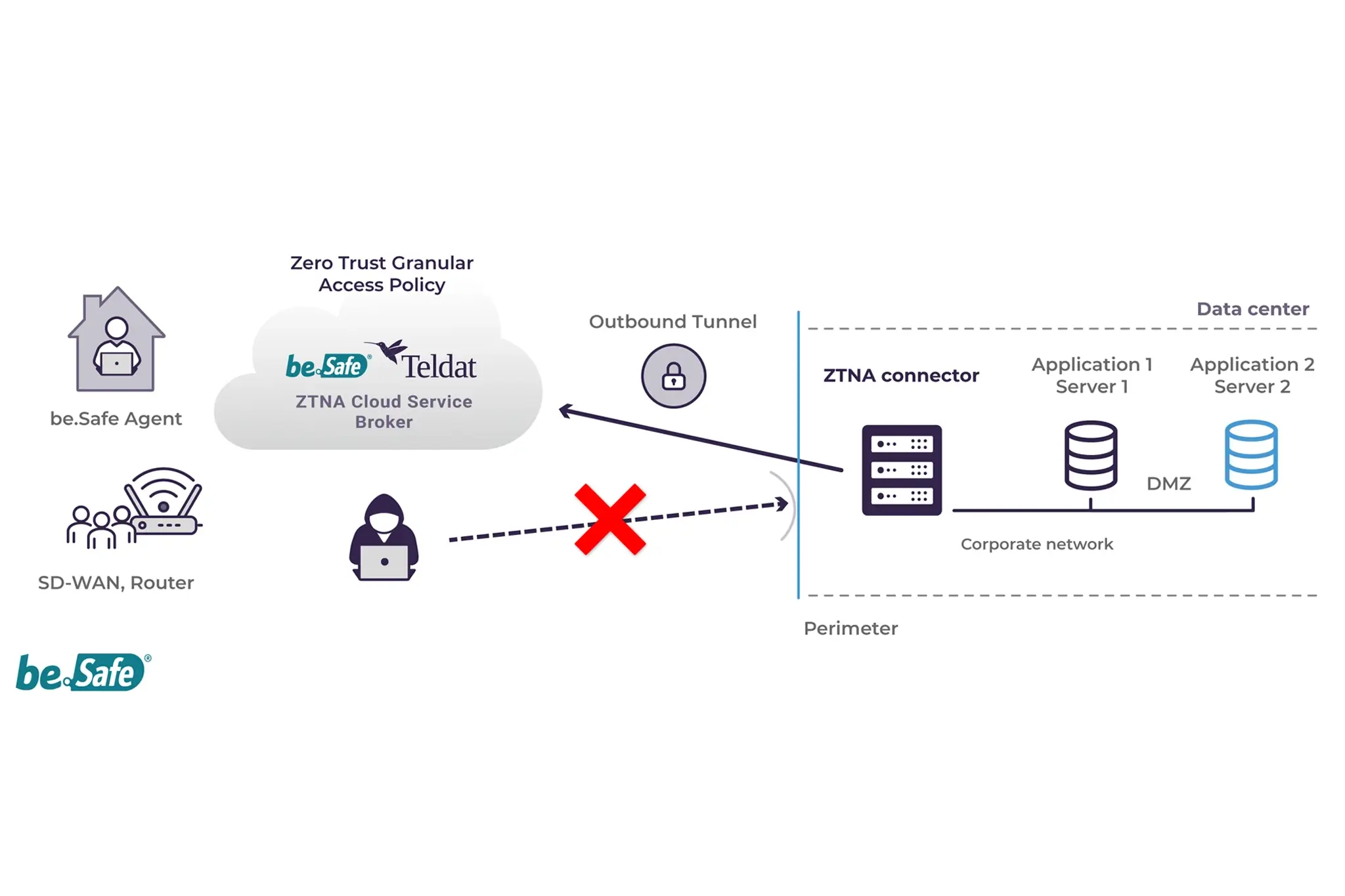
Instead of granting broad access to the network, ZTNA provides granular and controlled access only to specific applications or services. This dramatically reduces the attack surface and limits the impact of potential incidents. ZTNA also introduces continuous verification throughout the session. Access is not granted once and left unchecked; it can be adapted or revoked based on changes in context, such as device status, location, or detected risk level. As a result, security becomes a dynamic process rather than a static control.
In addition to strengthening security, the ZTNA model also improves the user experience. Access to required applications is provided transparently, without exposing services to the Internet or forcing users to connect to full network environments they do not need.
Overall, ZTNA represents a modern approach to secure access designed for today’s hybrid and distributed environments. It prioritizes identity, context, and the principle of least privilege to protect corporate resources more effectively while addressing the real needs of organizations.

Teldat´s ZTNA Solutions & Products
Teldat’s Zero Trust Network Access solution
Teldat’s ZTNA solution offers a comprehensive and modern approach to protecting access to corporate applications and resources under a Zero Trust model. Its goal is to ensure that each access request is explicitly verified, continuously monitored, and limited to only what is strictly necessary, regardless of where the user, device, or application is located.
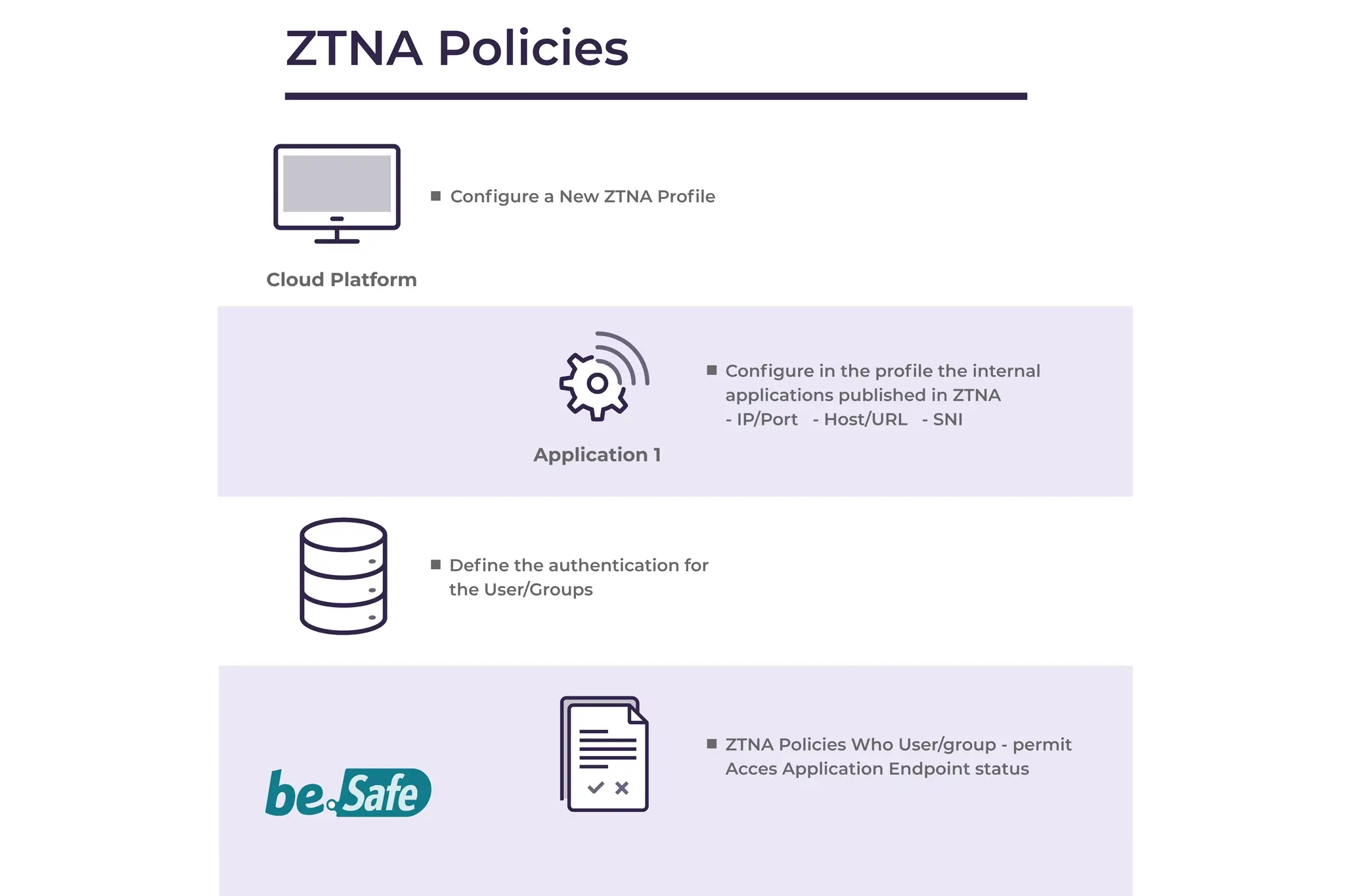
A comprehensive ZTNA solution aligned with market needs
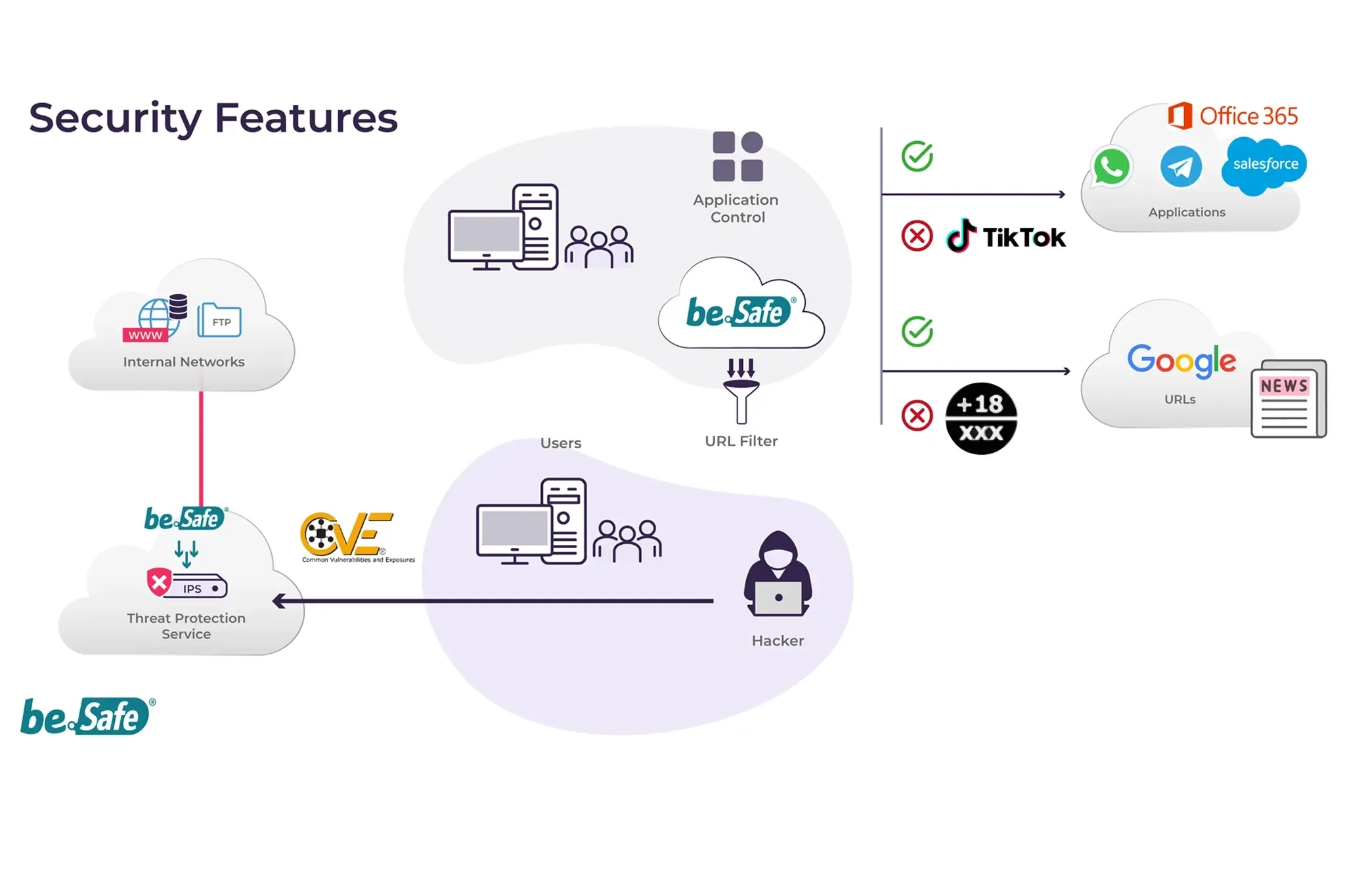
Teldat’s ZTNA proposal integrates the essential capabilities of a modern ZTNA solution: strong authentication and session control, continuous endpoint posture assessment, and dynamic context-based access policies. Thanks to this approach, access can be granted based on real-time data such as user identity, device status, location, time, or risk level.
In addition, the solution incorporates advanced security capabilities such as SSL inspection, intrusion prevention policies (IPS and IPS OT), and data loss prevention (DLP) controls, reinforcing access protection without compromising the user experience.
Integration with the security ecosystem
Teldat’s ZTNA solution is designed to integrate seamlessly with the organization’s security ecosystem. It connects with identity providers (Active Directory, LDAP, IdP such as Azure AD or Okta), EDR/XDR solutions, SIEM platforms, CASB, and PAM systems, enabling context sharing, consistent policy enforcement, and centralized visibility and auditing.
This integration facilitates application or service-level microsegmentation, preventing broad network access and reducing the attack surface, even in complex and distributed environments.
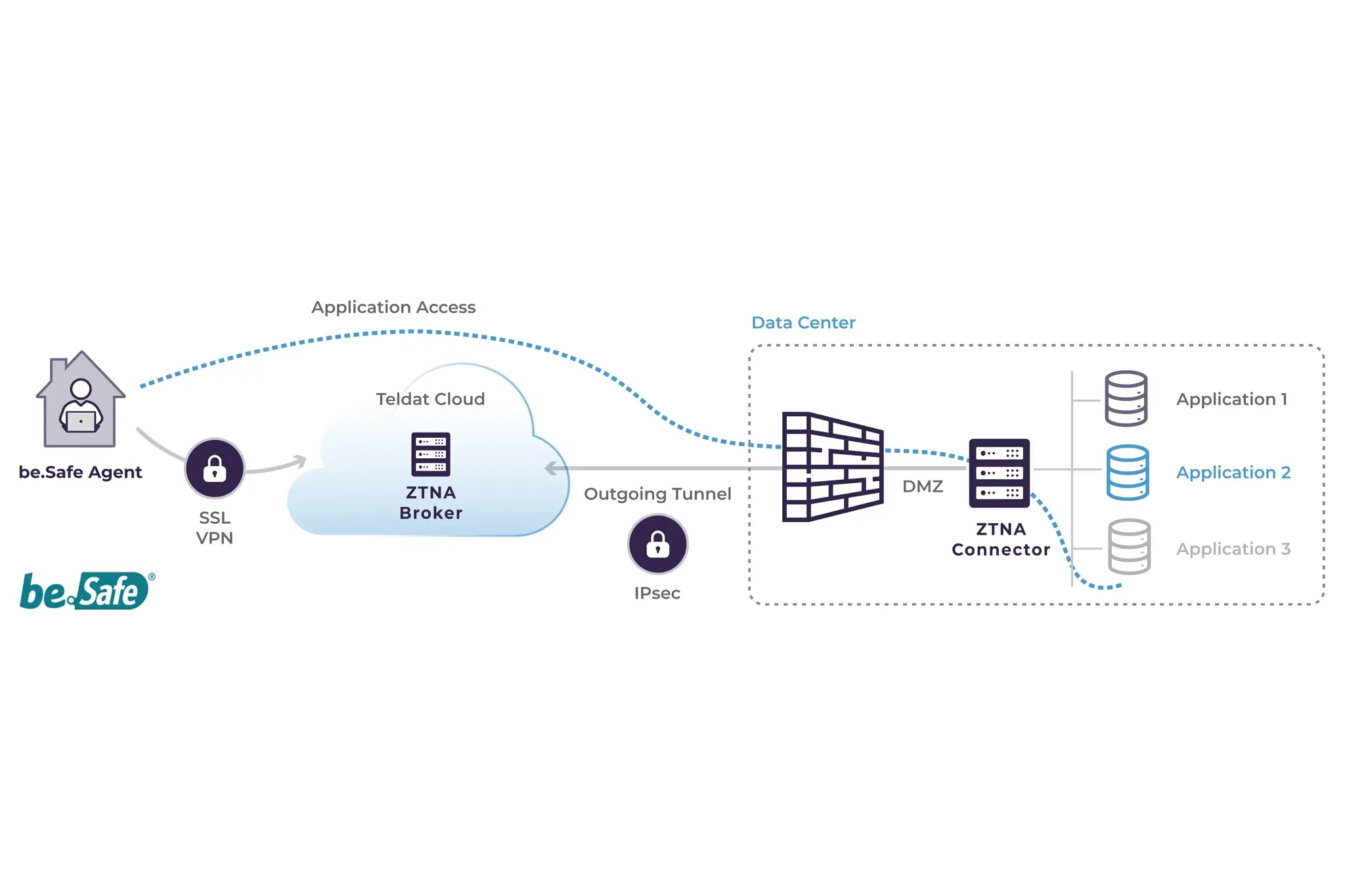
Flexible architecture and key components
The solution is based on a modular architecture that can be adapted to different deployment scenarios:
- be.Safe Agent is installed on user devices and securely establishes the necessary tunnels to the ZTNA platform, ensuring a transparent access experience.
- ZTNA Connector is deployed within the customer’s network and provides visibility into applications and connection points, securing user access to internal resources.
- ZTNA Broker acts as a central control point, receiving tunnels, evaluating access policies, and blocking any connections that are not explicitly authorized. It can be deployed both in the cloud and on-site.
A solution designed for real-world environments
The combination of advanced ZTNA capabilities, integration with the security ecosystem, and a flexible architecture allows Teldat to offer a solution that can be adapted to cloud, hybrid, or on-site environments. This enables organizations to adopt a Zero Trust model progressively while maintaining control, visibility, and regulatory compliance without relying on a single deployment model.
Teldat´s ZTNA Use Cases
Secure remote access without VPN’s
Secure remote access to corporate applications based on identity and continuous verification, without exposing the network or relying on traditional VPN’s.
Controlled third-party access
Suppliers and partners are granted temporary and restricted access to specific applications, with granular control, full traceability, and automatic re-provisioning.
Secure remote access without VPN’s
Secure remote access to corporate applications based on identity and continuous verification, without exposing the network or relying on traditional VPN’s.
Challenge
Remote working and access from external locations have become a permanent necessity for many organizations. However, traditional VPN-based models extend the network perimeter and give connected users too much access. This increases the risk of unauthorized access, lateral movement, and exposure of internal resources that are not necessary for the task at hand.
In addition, VPN’s often create user experience issues, operational complexity, and scalability challenges, especially as the number of remote users grows or when accessing applications distributed across different environments. Organizations need a more secure, granular, and simple remote access model that protects applications and data without compromising productivity or introducing unnecessary risks.
Solution

Teldat’s Zero Trust Network Access solution provides secure, identity-based remote access, eliminating the need to expose the corporate network or grant broad access. Each user can access only authorized applications after explicit identity, context, and device-status checks.
Access is established transparently, without the need for traditional VPN’s, and is continuously evaluated throughout the session. This reduces the attack surface, improves user experience, and allows organizations to precisely control who accesses which resources, from where, and under what conditions.
Why Teldat?
Teldat combines a robust Zero Trust model with a simple and controlled access experience. Its ZTNA solution protects remote access without adding complexity, integrating with the existing security ecosystem and adapting to hybrid and distributed environments.
Controlled third-party access
Suppliers and partners are granted temporary and restricted access to specific applications, with granular control, full traceability, and automatic re-provisioning.
Challenge
Organizations increasingly collaborate with vendors, partners, and third parties who need access to internal applications to provide services, perform maintenance, or work on specific projects. Managing this access securely is challenging, as it often involves shared credentials, permanent access, or manual configurations that are difficult to audit.
Traditional approaches make it difficult to restrict access to the necessary resources for a specific period of time. This increases the risk of unauthorized access, misuse of credentials, or active access lasting longer than necessary, posing a significant risk to security and regulatory compliance.
Solution

Teldat’s ZTNA enables specific, temporary access for third parties, based on identity and contextual policies. Vendors only access authorized applications, with no visibility into the internal network and no need for permanent credentials or VPN’s.
Policies can be defined by time, user, and context, allowing automated provisioning and revocation of access. This facilitates secure, controlled, and auditable collaboration, while reducing risks and simplifying the operational management of third-party access.
Why Teldat?
Teldat’s ZTNA solution facilitates secure third-party access management through a practical and easily automated approach. It allows organizations to maintain full access control, improve traceability, and comply with security and audit requirements without adding operational complexity.
On-site ZTNA for regulated environments
Full on-site Zero Trust access for regulated industries, with strict user control and minimal access to critical applications.
Challenge
In highly regulated sectors such as banking, many organizations cannot rely on cloud infrastructures to manage access to their critical systems. Data sovereignty, regulatory compliance, and operational control requirements require access services to remain within the organization’s own infrastructure.
In addition, some user profiles with very limited functions (such as cashiers or office staff) only need access to a small set of corporate applications. With traditional models, enforcing this level of restriction without exposing the internal network is complex and costly, increasing the risk of unauthorized access and complicating security audits.
Solution
Teldat’s ZTNA solution allows the access broker to be deployed on-site, ensuring that the organization’s infrastructure remains fully under its control. Under a Zero Trust model, users only access authorized applications and cannot view the corporate network or move laterally to other resources.
Policies are applied based on identity, context, and role. This allows predefined user profiles (such as cashiers) to be granted very limited access, restricting their operations to strictly necessary systems. This approach strengthens security, simplifies regulatory compliance, and ensures full access control without relying on external cloud services.
Why Teldat?
Teldat offers one of the few ZTNA solutions that allows the broker to be fully deployed on-site. This makes it an ideal choice for regulated industries that require Zero Trust security, granular control, and strict compliance without sacrificing operational flexibility.
Read our latest Blog Posts
Cybersecurity for Industrial Environments
In recent years, industrial environments have undergone significant changes. Industry 4.0 has led to numerous advancements in production and operations, but it has been primarily defined by the emergence of new technologies that were previously absent. Automation and...
NIS 2 – Cybersecurity-related legislation in 2024
Now that 2024 is about to end, let’s have a look at this year’s cybersecurity highlights. Changes in legislation like NIS 2 (both in countries and supranational bodies, like the EU) probably rank amongst the most important. All of these changes in legislation have...
Network Behavior Analysis: Key to guarantee Security and Performance
In an increasingly complex and interconnected technological environment, the performance and safety of IT networks are key aspects for any organization. Traditional monitoring and protection systems are not enough to respond to advanced threats or optimize the use of...