BLOG

AI Under Attack: A Threat Evolving at the Speed of Technological Innovation
In 2025, Artificial Intelligence (AI) systems are not only tools for productivity, automation, and advanced analytics—they have also become new attack vectors for cybercriminals. From data manipulation to direct model exploitation, the threat landscape is evolving as rapidly as AI itself. For professionals in cybersecurity, cyberdefense, and technology consulting,...
Kategorien
Microservices & its advantages
The idea behind Microservices has been with the software industry and developers for about six to seven years now, and it´s definitely a current buzz term which is being heard more and more in the industry. However, in global terms it´s a relatively simple concept. A...
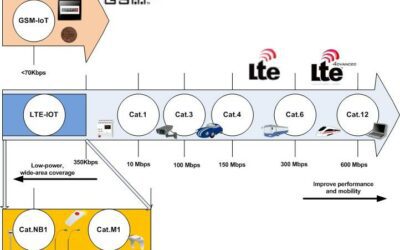
Emerging Low Power Technologies
To support the further growth and development of the Internet of Things (IoT) the mobile industry is developing and standardising a new class of GSM technologies focused on IoT, which is called Low Power Wide Area (LPWA) networks. These technologies enable the new IoT...
More and more people commute to work
The number of commuters rises to record high. According to an analysis by the Federal Institute of Research on Building, Urban Affairs and Spatial Development (BBSR), the number of commuters in Germany has peaked at sixty percent, compared to 53 percent in 2000. On...
Big movements in the sector
As I have done in previous years around this time, I would like to take this opportunity to summarize some of the most important issues we have encountered in 2017. This year is proving to be a very interesting year for the telecommunications sector. First of all, the...
Access to guest networks
Nowadays, all companies provide their customers with Wi-Fi in some form or another. We find it in shopping malls, airports, restaurants, offices and even on transport. It is fair to say that Wi-Fi has become a commodity. Most customers want to connect to Wi-Fi...
5G: How it will change our lives
The advent of 5G technology signifies the start of an even more globally connected society, a completely digital society. This technology, expected to be implemented in 2020, will change the way we interact with each other and objects, allowing us to be permanently...
Digital Transformation from a business perspective
Over the last years colleagues have written blog posts on digital transformation and the new technologies within the telecommunications industry that are accompanying the phenomenon. However, I would like to take a step back and look at the digital transformation from...
Power electronics in telecommunication equipment
The application of power electronics to communications devices has to do with the processing of the electrical input power using semiconductor devices and reactive elements. Thus, the raw input power is processed according to a control input that conditions the output...
WannaCry – Bitcoin – Crime
The first and so far the only time I was personally involved, (or to be more precise my son who at that time was eleven years old), in a cyber-attack by ransomware was in 2012. The computer of my son was apparently blocked by the Federal Criminal Police Office due to...
Dynamic DNS Update – Teldat
Nowadays, if you check the public IP address with which you access the Internet, you will find that it often changes. This is due to the chronic shortage of IPv4 addresses, which are insufficient to cover current service demands. ISPs, therefore, often assign dynamic...
First SHA-1 collision
In February this year, a team of researchers both from Google and CWI Institute in Amsterdam announced that they were able to generate two PDFs documents with different content that would hash into the same SHA-1 digest. This may lead to a big problem in security that...
EMC electromagnetic compatibility and signal integrity
The growing number of electronic devices and wireless technologies providing ever-increasing performances and speeds requires a set of common standards to ensure EMC electromagnetic compatibility. Ever since Michael Faraday’s discovery in 1831 of the phenomenon of...