BLOG

A New Path to IPv6 Networks
The shortage of IPv4 addresses has accelerated the move toward IPv6. With roughly 4.3 billion possible addresses (32 bits), IPv4 can no longer meet the needs of modern connected devices. IPv6, by contrast, uses 128 bits—roughly 340 sextillion addresses—providing virtually unlimited capacity for growth. Over the past few decades, several methods have been developed...
Kategorien
CAD / CAM / CAE technologies
The acronym CAD comes from the English expression Computer Aided Design. It involves the use of computer technology to aid in the design of a product. In the case that concerns us now, it would involve designing housings for communications devices. In short, CAD is...
Even more changes in 2020? SD-WAN?
With just a glimpse of how the telecommunications and in particular the networking market has developed over the last year, it can undoubtedly be seen that a snowball effect is occurring as the markets and the technology within these markets are rolling and becoming...
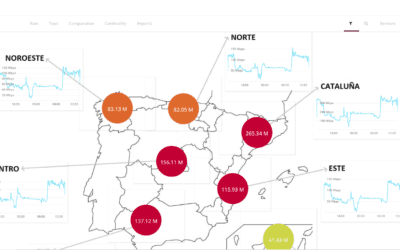
Love is blind, but your SD-WAN network isn’t
Identifying performance issues in WAN networks has always proved a challenge for IT professionals. In this sense, having advanced network visibility and monitoring tools is absolutely essential. Communication problems have an impact on applications and must,...
Open Data – contributes to Smart Cities
A few weeks ago, we blogged about the importance of Smart Cities to promote smart sustainable cities. Half the population worldwide now lives in big cities, and this figure is expected to rise over the next ten years. Recent UN studies show that urban centers consume...
Protocolos y variantes CSMA
Si dividimos un sistema de comunicación genérico en sus partes más “simples” podemos distinguir cuatro elementos: Un emisor, un receptor, un mensaje y un medio o canal para comunicarlo. Uno de los problemas que surgen desde que se establece la comunicación es el...
Intent Based Networking
According to the prestigious consulting firm Gartner, Intent-Based Networking System – IBNS - technology will be the go-to tool for managing data networks in a few years’ time. It is an evolution of Software-Defined Networking SDN / SD-WAN. If we take into account...
5 trends that will transform telecommunications in 2020
We are approaching the end of 2019 and the beginning of a new decade in which we are expecting amazing technological innovation capabilities. The last few years have seen repeated reports of trends, with much talk of 5G, cloud services, blockchain, edge computing,...
Peer-to-peer networks
Cryptocurrencies have been hailed as one of the greatest technological revolutions of recent years. Bitcoin is the pioneer and best-known of them, but there are hundreds more – each with different characteristics, objectives and technologies behind them to make them...
Segmentation in SD-WAN
The SD-WAN market is gaining more and more strength; software-defined and managed connectivity solutions provide ever more possibilities and functionalities to adapt to the reality of business networks. One of the key aspects that all companies value is security. In...
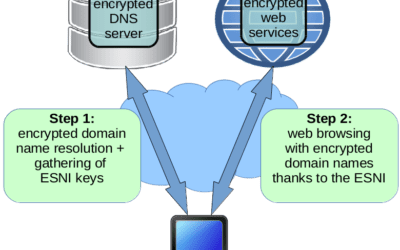
Moving towards a fully encrypted Internet: DNS encryption and ESNI in TLS
Web browsing first began as a system lacking in privacy that allowed users to view simple content in text mode. Since then, the service has evolved in both functionality–allowing you to view complex designs–and in its access methods–said web content can be downloaded...
High-speed Internet from space: The Starlink network
Accessing the Internet from space is not new, with many companies (OneWeb, Space Norway, Telesat, etc.) now offering it. More recently, however, a new participant has emerged on the scene promising something different – Starlink. SpaceX’s plan is to create a network...
DTLS security over UDP
DTLS (Datagram transport Layer Security) is a protocol that provides privacy for UDP communications. To understand DTLS, you first need to understand UDP. UDP (User Datagram Protocol) is a transport layer protocol based on the exchange of datagrams (encapsulated in...