BLOG

Private 5G networks for companies, public sector and operators
The adoption of a private 5G network has become a strategic pillar for companies, public institutions, and operators seeking secure, high-performance communication infrastructures under their full control. Unlike public networks, a private 5G network combines the flexibility of wireless connectivity with complete control over management, security, and traffic...
Kategorien
Web components – understanding the technology
Web Components is a standard introduced by the W3C for creating new elements for the web. It also allows developers to easily reuse and extend both the developed components and native elements. As they are part of the browser, no external library like jQuery is...
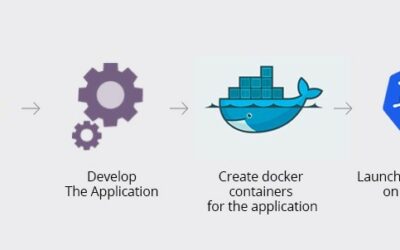
Microservices, Dockers and Kubernetes
Many companies today are opting for microservices-based architecture. And this most certainly has to do with the fact that microservices are a perfect complement to SDN/SD-WAN technology, allowing the modules that make up the applications to be implanted in numerous...
Fixed Wireless Access – Why 5G-FWA can succeed
In my previous blog post last week on 5G, we saw how Fixed Wireless Access (FWA) is considered a cornerstone use case for 5G and a new source of revenue stream for both MNOs and CPEs manufacturers. But if LTE is already capable of reaching extremely high Broadband...
Fixed Wireless Access – primary use case for 5G
Fixed Wireless Access has huge opportunities and challenges for the Telecom Industry with the deployment of the 5G system, but why is so important? Up to now, LTE is still considered the fastest developing mobile technology ever. Since its launch in early 2010, it has...
The importance of SD-WAN for SMEs
Small and medium enterprises (SME’s) make up an increasing percentage of existing companies. As a result, they account for almost all of the business fabric worldwide. However, given their limited size, their budget for human resources, technology, safety, and...
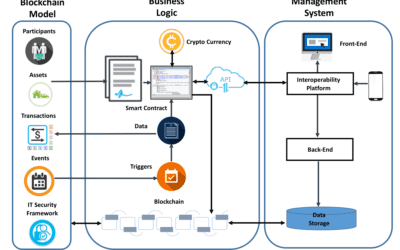
How did Blockchain commence?
As we previously mentioned in an article published in June 2019, the Bitcoin did not create a new computer technology but integrated a series of pre-existing techniques in a revolutionary manner. The possibilities this protocol could bring were soon condensed in a new...
React, a new technology
Launched in 2010 by Facebook, React is an open source technology that became popular when Facebook bought Instagram in 2014 and launched this new language. Facebook, together with a free software community made up of more than 1,000 developers, is in charge of its...
SD-WAN in Latin America
It’s no secret to anyone that the concept of SDN/ SD-WAN has been gaining ground over the past four years. This is in direct response to a clear need to erase geographical boundaries and improve visibility, control, availability, performance, scalability and security...
All gigabit accesses are born (free?) and equal…
When gigabit accesses are mentioned, the first thing that comes to mind for most of us (especially in Spain) is a fibre-optic access network for speeds beyond 50Mb. Carriers take the optical fibre to your home, install an ONT and that’s it. Customers can choose...
Uptime is down. Long live the fleeting!
Since the early days of systems administration, a god has hovered over server rooms: uptime. uptime tells us how long a server has been on, which indirectly indicates how long it has been since it had a problem requiring a reboot. Operating systems have always had...
Why Apache Kafka?
These days, numerous applications follow a microservices architecture. And many applications manage large amounts of data (user activity on the application, logs, metrics, etc.) that are constantly travelling back and forth between microservices. This can produce a...
Private LTE networks
Up until now, we have talked extensively about 4G and 4G+ (4G Advanced) mobile communications, and even more so about the upcoming 5G networks. However, I would like to take this opportunity to address mobile wireless technologies based on a private LTE network. As...