BLOG
Quantum computing and cybersecurity
We are currently in the midst of a quantum computing revolution that threatens to break all processing limits. When we apply these concepts to cybersecurity, we find potential quantum computing applications that can help us improve cybersecurity or crack it. Quantum computing can become a means to break one of the pillars of cybersecurity over the years: RSA-based...
Kategorien
Maximum performance routers; who gives you more?
The performance, power, energy consumption and useful life of routers are all measurable factors in product testing. The data, however, depend on the conditions under which manufacturers carry out the tests. Transparency is vital! After 10 years and more than 400,000...
DMVPN vs Mobile IP
Nowadays, there are more and more applications running on a mobile environment such as, M2M, services for passengers, telemetering, etc… These applications often rely on several wireless access technologies (LTE, 3G, Wi-Fi, Satellite…) to implement the connectivity to...
Communication is everything
Communication is everything and a crucial part of our daily life. Some people go even further and say that it is everything. The American author John Gray who wrote “Men are from Mars, Women are from Venus” is strongly committed to this theory as he advises that...
The 5th Mobile Generation: Research on the Future Internet
Mobile Internet becomes more and more popular. Whereas mobile Internet has only been used for email checking, it is now used for the same applications as the Internet by cable: surfing the Internet, playing online games, listening to music or streaming videos and...
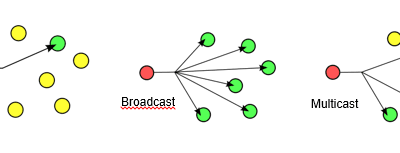
The importance of Multicast mechanisms
What does multimedia streaming means? Multimedia streaming is increasingly present in our lives. Streaming allows a user to view or listen, to this content without previously downloading it. A user connects to the server which in turn sends the multimedia content. ...
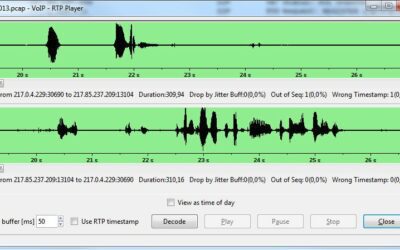
VoIP Security
Some countries switch off their telephone network in the near future. ALL IP is as previously mentioned one of the main buzz words. The shift to VoIP has already started and now is the right time to ask ourselves: “Do we need VoIP security?” VoIP security in this...
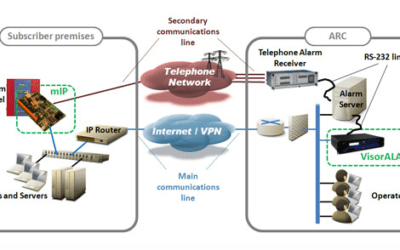
Smart Grid: The role of communications in the evolution of power grids
Smart Power Grids consist of the integration of power grid elements in advanced information systems to benefit power suppliers, distributors and consumers. These grids combine generation and distribution resources with demand through wide use of state-of-the art...
The first wireless LAN /WLAN
Everybody at least in Germany and probably in some typical German tourist centers knows the famous Song by Paul Kuhn “There is no beer on Hawaii” but not many people know that a network very similar to the wireless LAN available nowadays was already set up in 1969 by...
Positioning systems and mobility management
Years ago there was a revolution in overseas travel; we no longer needed to learn the routes of a nation because satellites were able to tell us our position in real time (using GPS). This technology was taken to another level by the professional market with the...
The ABC of SBC: definition, characteristics and advantages
The Firewall is the quintessential element providing network security when you need to interconnect with other networks, allowing outgoing traffic and blocking unsolicited incoming traffic. The Firewall is a necessary element, although it is insufficient for security...
Industry 4.0
Smart Factories, the Internet of Things, cyber-physical systems, mass customization - these are the futuristic-sounding buzzword when it comes to Industry 4.0. The term "Industry 4.0" provides information on all the hopes that are placed on the subject. It indicates a...
Rest architecture: The provision of centralized services
For a number of years now we have been constantly bombarded by the idea of the cloud, where there is room for virtually everything, whether it is a private cloud or a public one, with servers installed at the client’s head office or in large data centers around the...