BLOG
Quantum computing and cybersecurity
We are currently in the midst of a quantum computing revolution that threatens to break all processing limits. When we apply these concepts to cybersecurity, we find potential quantum computing applications that can help us improve cybersecurity or crack it. Quantum computing can become a means to break one of the pillars of cybersecurity over the years: RSA-based...
Kategorien
Wireless LAN Controller in the Private Cloud
Whether it’s the residential sector or comprehensive installations within offices, to highly sophisticated applications and even beyond, by now wireless networks can be found in almost all market segments. Wireless LAN has become far more than a mere network to supply...
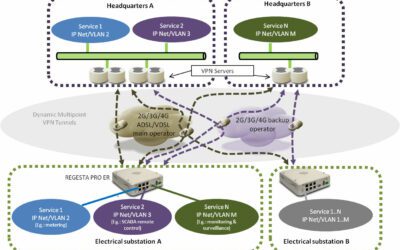
Possibilities of the Smart Grid
Nowadays the whole electric grid is rapidly changing worldwide. Generation quickly becomes distributed through the use of new renewable energy sources (primarily wind and solar based). Consumption also takes new forms, as users develop new needs through the use of...
Can 4G/LTE become a main line connection?
Perhaps this question has to be clarified somewhat. Indeed, slower and more mature cellular lines 2G and 3G lines are already main line connections in certain scenarios, especially in those segments which are not so dependent on large bandwidth, but at the same time...
Alphabet – ICT environments
Or, is there? Had you ever thought about it? Is it important? Maybe not, but I bet you that a vast majority of us have at least lived a moment in which we have strongly wished the alphabetical list by which we were being called was in a different order. Or that our...
Heartbleed attacks and Internet security
Our daily data traffic on the Internet has reached dimensions which can hardly be put into numbers. For example, in June 2014, an average of 1.7 Tbit/s of data has been transmitted at the German DE-CIX (the largest Internet exchange point worldwide, situated in...
Hybird solutions: a single device for every branch office
All of a sudden, the office has become a very complicated place with a lot of electronic devices that need to be configured, maintained, powered, secured, actualized, and wired (or maybe not, because they are part of a WLAN network). Even though most of the...
Router and Server for onsite applications
It is quite obvious to say that corporate communications have evolved. Not so long ago, a few decades ago, “dumb” terminals were connected to a mainframe. A significant evolution followed with the introduction of X25, Frame Relay and ISDN. We could say it had the...
What to expect from Wi-Fi 802.11 ac?
Currently there is a lot of noise in the press regarding the new so called Gigabit Wi-Fi 802.11 ac standard. Of course the upgrade to 802.11 ac has some technical advantages, but even though, is now the right time to upgrade your enterprise network or is the new...
Internet on the rails by Teldat
Cellular networks allow new services by making Internet access ubiquitous. Their increasing coverage, reliability and speed allow businesses and end customers alike to take advantage of new possibilities, although at the same time they increase dependence on Internet...
Securing Business via Resilience networks
One can safely say that currently businesses of any kind require WAN resilience, as part of their network set up, because independently of a company’s size (SME’s or Corporations) or business environment, WAN outages hit hard. There is no doubt in that. Some years...
A start, that is actually a boost.
This is the first post of our blog “Communicate with Us”. For Teldat and everyone who make up the company, this is the beginning of an important project. Some say that the beginning of something means half the effort, but for us this is not so, as we have been...