BLOG
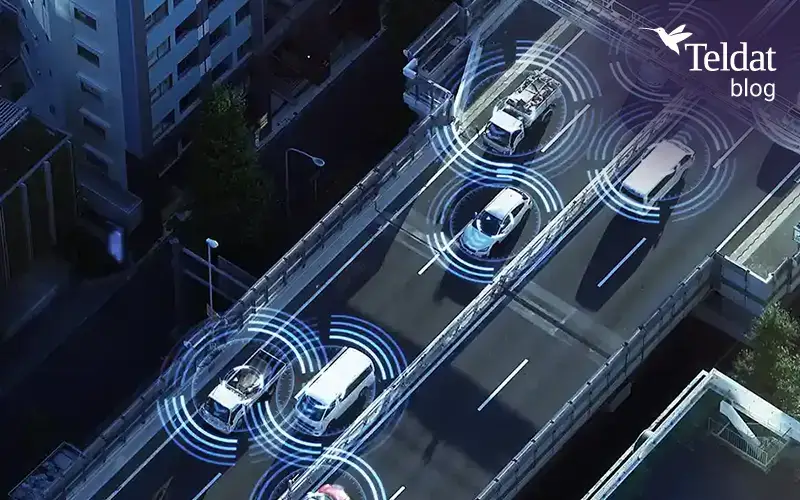
Critical fleets are only as resilient as their connectivity
In critical fleet operations, vehicles aren’t standalone units anymore. Each one is a mobile part of a bigger digital system that relies on continuous, secure, real-time communications. Video streams, telemetry, location data, remote diagnostics, coordination with control centers, and vehicle-to-vehicle / vehicle-to-infrastructure links, only work if connectivity...
Kategorien
The advantages of Wi-Fi 6 – 802.11ax
The Wi-Fi 6 technology set out in the 802.11ax High Efficiency (HE) standard is the natural successor of the wireless Wi-Fi 5 technology or 802.11ac standard, known as Very High Throughput (VHT). This new implementation has been designed to work in high user density...
Roboethics as a fundamental part in the development of autonomous vehicles
Environmental digitalization represented a major step forward for some industries like the automotive industry, telecommunications, agriculture and banking. And these are also the ones that are set to undergo the most changes in the coming years. One of the most...
Towards a Thin CPE
It has been more than 10 years since desktop virtualization, generally found under the acronym of VDI technology, Virtual Desktop Infrastructure, was proposed as one of the main technological drivers for providing greater flexibility, efficiency and control to the...
Anywhere Operations
After a year as turbulent as the past one was, it is interesting to see the latest trends identified in the world of new technologies, the momentum of which has been key to continuing to maintain the business fabric worldwide. It was the year of teleworking, of...
Intelligent Automation: benefits for enterprise & organizations
The telecommunications industry continues to be at the focus of growth, innovation, and disruption as a result of new technologies that continue to filtrate the market. The cut-throat competition and growing demand for seamless connectivity are the biggest challenges...
Trends in 2021: telecommunications will bring vast, social, economic & industrial changes
When clock struck twelve midnight on New Year’s Eve this year and we went into 2021, many of us thought… “that’s it, we have finally left behind us, the disastrous year of 2020 and we start the year 2021”, hoping that normality will return as soon as possible....
Teldat launches 5G web page
Teldat M8Smart-5G and Teldat-5Ge products in Teldat’s new 5G web page, offer advanced solutions for corporate services
Smart Rural 21 & 5G: The challenge of connecting rural areas
The movement of people in search of opportunities not available to them in their birthplaces has always been taking place. The last most significant migrations of people in Spain for example were: The rural flight, driven by the industrial revolution, which...
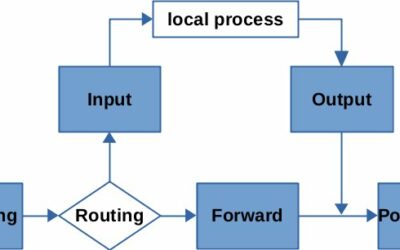
Connecting some of the dots between Nftables, Iptables and Netfilter
When it comes to packet filtering on Linux, Nftables (a successor to Iptables) has matured sufficiently in recent years for it to be considered the default tool to use today. However, Iptables is still widely used in modern systems (e.g., Debian buster), with it...
Ensuring security in corporate environments
Due to the radical change in the way we work in IT caused by COVID-19, communications and IT professionals and administrators have been forced to implement or improve necessary mechanisms to ensure security in corporate environments while maintaining their...
Log centralization in microservices with Fluent Bit
Nowadays, it is quite common for systems to be made up of many like subsystems and Fluent Bit. These include small programs that work together, full Operating Systems and proprietary applications. This growing number of subsystems needs maintenance to assess their...
be.SDx Corp: Teldat’s SD-WAN corporate solution
Teldat’s SD-WAN solution for corporate networks has a new section on the Teldat’s website… “be.SDx Corp”