Now that mass and social media are booming, it is normal for marketing to take over and for technological terms to become more trivialized and popular. We are all familiar with cloud computing, now linked to edge computing, blockchain, the metaverse, AI, etc. However, the concept that has taken this year by storm is cybersecurity, and it would be unwise not to analyze it in depth.
Now that mass and social media are booming, it is normal for marketing to take over and for technological terms to become more trivialized and popular. We are all familiar with cloud computing, now linked to edge computing, blockchain, the metaverse, AI, etc. However, the concept that has taken this year by storm is cybersecurity, and it would be unwise not to analyze it in depth.
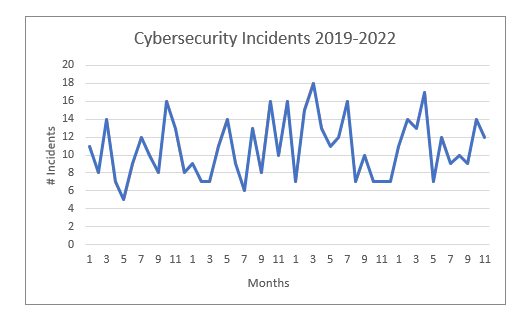
Source: Cybersecurity incidents causing more than one million dollars in losses during 2019-2022.
No wonder the term is so trendy! Since 2019, cyberattacks causing more than a million dollars in losses have annually increased by (at least) 3%.
How can a cyberattack be so harmful? Those targeting operating systems related to critical infrastructures (i.e., those quantified in tangible terms, such as money, or intangible terms, such as brand image) are the most dangerous.
Fortunately, security measures also improve every year and, in order to protect these critical infrastructures, we have OT cybersecurity.
OT cybersecurity?
Whenever we discuss cybersecurity, we first think of the corporate and IT environment: “they’ve hacked a celebrity’s cellphone”, “hackers have accessed a web portal and disclosed the details of every user”, etc. However, it is crucial to apply this term to OT (i.e., industrial networks and systems).
Why do we have to worry about keeping a safe logical environment in OT systems when they benefit from high physical security, are very predictable, structured and are often located in places that are hard to access?
- While IT ensures the confidentiality, integrity and availability of systems and data, OT environments control and monitor physical processes, devices, and infrastructures. Both seem to be worlds apart, but the need for Big Data and data analysis in OT environments means these infrastructures have to be increasingly present in IT systems and networks. This opens these systems to threats from the IT world, despite them having weaker protection measures.
- Generally speaking, all OT systems share a key characteristic: they often provide support to critical infrastructures (not only from a service standpoint, but also when it comes to protecting human lives). In these infrastructures, availability is the most relevant safety requirement.
- For instance, if the operation of an electric grid is blocked at some level, this could cause incalculable losses in terms of money and corporate image.
- During a war, critical infrastructures are also the target of cyberattacks given their importance for human survival.
- Something as mundane as the rail service can serve as an example. In the aforementioned graph, a cyberattack against the Danish rail service in November 2022 resulted in trains being halted for hours.
- Another example of an attack carried out in 2022 against a critical infrastructure is when hackers targeted the biggest natural gas distributor in Greece (DESFA). This caused serious disruptions and the disclosure of sensitive data.

Key points in OT cybersecurity
The most serious vulnerability stems from the misalignment between the ruling characteristics of an OT environment (e.g., a less dynamic architecture and failure to adapt to constant changes) and the criticality of the services it supports. OT cybersecurity is, therefore, essential and must be a top priority for companies with an OT infrastructure.
As a result, new safety solutions aimed at integrating consolidated solutions and security providers are popping up. To reduce complexity and be able to view all devices (IT and OT) in a centralized manner, organizations should combine IT and OT solutions for fewer providers. Integrated security solutions reduce risks and improve operational safety and efficiency.
We must take a different approach to OT cybersecurity and understand that we cannot deal with it the way we do with IT systems. It is a paradigm shift, involving more than a specific set of signatures (different criticalities, deployments, updating, operation, scenarios in the event of failure, etc.).
What functionality must we take into account when rethinking OT cybersecurity?
OT systems are complex. They have been developed and implemented over decades (their depreciation period is very long because they require a large investment) and patched so many times that no-one knows exactly how everything works. In addition, OT resources can be distributed across different locations that are hard to access. Thus, providing a tool that is capable of finding assets within the OT network is key (despite there being no easy solution for it).
Given the aforementioned convergence between IT and OT networks, any cybersecurity solution must be able to resolve threats from both worlds in a unified manner and cover any scenarios that could impact this new architecture.
IT cybersecurity is geared towards protecting central company systems but, when it comes to protecting critical infrastructures, it falls short: the closer safety measures are sent to each network node, the better. Having next-generation firewalls in perimeter nodes is essential to build a multilayer OT cybersecurity system. This is why an OT cybersecurity system must be able to offer IDS /IPS capabilities to network devices and centralized functions (if desired).
Unfortunately, when it comes to industrial systems, installing a security patch in end devices is impossible or too expensive. For this reason, it is crucial that the security system allows patches to be installed in the network so that individually accessing each device is not necessary (meaning changes can be directly applied to the data network).
Learning whether an IT or OT cybersecurity system has signatures is easy to verify, but this kind of system can also be vulnerable (for instance, if it hasn’t been correctly updated). Zero-day attacks cannot be identified by these systems, meaning additional tools like AI – Artificial Intelligence models are necessary to detect anomalous activities in an OT network. Using a Network Traffic Analyzer – NTA’s and an AI engine in industrial systems is highly recommendable (since they are far more stable, reliable, and predictable than IT networks).
Conclusion
Fortunately, cybersecurity solutions are taking OT environments into account during the design and coverage stages. This means that many of the vulnerabilities stemming from the definition criteria used while creating these systems and environments can be corrected.
We have touched on some fundamental concepts regarding OT cybersecurity – namely, network node self-discovery, centralized and edge security, IDS/IPS with signatures, or the implementation of NTAs and AI models to learn how the network behaves in OT environments. However, this has been no more than an introduction.
At Teldat, we have worked hard to offer an OT and IT cybersecurity solution. be.OT provides specific functions for these environments and is very useful in order to protect critical infrastructures managed by industrial protocols within OT networks.
Source & other points.
- https://www.techtarget.com/searchitoperations/definition/IT-OT-convergence
- https://www.techtarget.com/iotagenda/tip/Operational-technology-vs-information-technology-explained
- https://www.washingtonpost.com/politics/2022/07/25/iran-israel-cyber-war/
- https://www.csis.org/programs/strategic-technologies-program/significant-cyber-incidents