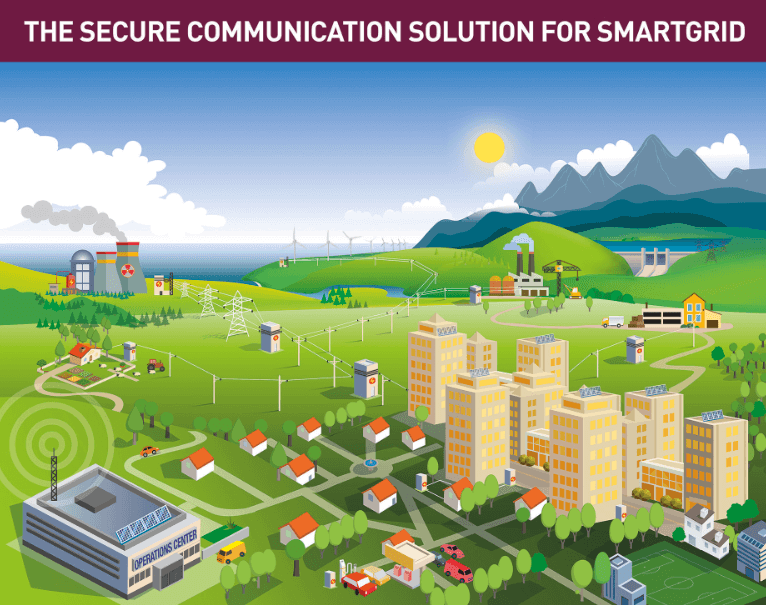
 When deploying a SmartGrid network, one of the most important and demanding issues one must take into account is to ensure said network is secure, reliable and stable.
When deploying a SmartGrid network, one of the most important and demanding issues one must take into account is to ensure said network is secure, reliable and stable.
The current state of the art technology allows you to activate security mechanisms in different network communication devices, so guaranteeing data confidentiality, integrity of transmitted data and availability of said information.
But, how can we protect a network made up of hundreds of thousands of remote points? How can we ensure data confidentiality when transmitting over third party networks (carriers)? What can we do about security threats at each of these thousands of connection points?
Communications devices serve as nexuses between different remote electronic systems (telecontrol, metering, etc.), and communication networks (carrier networks, Optic Fiber, PLC, etc.) These devices often operate in critical and vulnerable locations, and many are subject to cyberattacks. However, when equipped with the appropriate mechanisms, these devices can substantially improve network security. Given how difficult it is to control and secure networks made up of thousands of connection points, it’s both necessary and advisable to activate security mechanisms in the network communication devices themselves.
Data transmission over third party networks can be safeguarded through VPNs (Virtual Private Networks) and data encryption protocols. Said networks are made up of tens of thousands of points, so it’s vital to implement mechanisms for both startup and subsequent management. DMVPN (Dynamic Multipoint VPN) is considered the best option to create a VPN and data encryption (IPSec) system in meshed networks containing a high volume of points requiring management.
There are other protocols and technologies that also safeguard the network from security threats. It’s strongly advised to use a combination of these to optimize security. The use of access lists, MAC filtering and 802.1X with extended authentication together with Radius and/or Tacacs+ are all excellent ways of achieving this.
In current SmartGrid network scenarios, intelligent meters, installed in residential and industrial areas, forward information to devices known as Telemetric Concentrators, which are generally installed in secondary substations (Transformer Centers). However, is it really safe to keep this information in thousands of points scattered across electrical networks?
With the currently available technology, both from the point of view of the reliability of communications, as well as saving to the cloud, wouldn’t it be more advisable to keep it stored in more secure and centralized locations?
The rapid advance in reliability, high availability and speed in communication networks, over both private (RF, PLC, Optic Fiber networks) and carrier paths, allows for mixed communication networks. This means that communication between remote devices (meters) and custom-made management systems is possible and can be used to save data in secure locations (similar to the way electricity companies save metering data but applied to private CLOUD concepts ).
It’s always advisable to keep this in mind when choosing technology/routers to be used in the network: This helps greatly in setting up security policies when both initiating network deployment as well as for one already deployed. Said devices should incorporate VPN techniques with the most advanced security, all demanded in professional areas and, obviously, based on market standards.
- Firewall & IPSEC, with all their variations.
- L2TP & L2TP/IPsec support.
- Multi-GRE with IPSec to implement VPN Multipoint WANs (DMVPN).
- Powerful traffic priority and bandwidth reservation policies.
- Access control for all devices based on Radius or Tacacs+ in all interfaces.
- Security mechanisms against threats in local interfaces: 802.11X, MAC address filtering, Access lists, etc.
All communication solutions Teldat provides for utility companies have the necessary WAN communication interfaces and securitization protocols for SmartGrid deployment.